Get Access Manager 11gRel2 PS2 installed in a day
Goal is to get OAM installed and configured in a day - with full control; that is without using the Installation Wizard.
Virtual Box
Start with Virtual Box. Allow plenty of memory (10GB), and disk (120GB).
Attach V33411-01.iso (Oracle Server V6.3) to the CD, and boot.
Minimal (not Basic server!) install, configure network with static IP addresses, X-Windows support.
Reboot. Test if you can ping a public server (e.g. oracle.com). If not - rework your settings until you can.
I needed to install nfs:
yum install mount.nfs
Also, disable SELinux (edit /etc/selinux/config, it is self explanatory)
Then, install prerequisites as described
here.
Give the oracle user a directory to install into:
mkdir /oracle
chown oracle:oinstall /oracle
Prepare
Start with the database, as described
here.
Then, run the Repository Creation Utility:
[oracle@oam admin]$ /mnt/orainst/Software/OFM/11.1.2.2.0/V43024-RCU_x86-64/rcuHome/bin/rcu
Install
In particular, install OUD, WebLogic, OHS and IAM suite. Later, configure the lot.
Install OUD
Described in an
earlier blog entry, but now the latest version.
It needs Java...
cd /oracle
tar xvf /mnt/orainst/Software/java/server-jre-7u76-linux-x64.tar
It will create an jdk1.7.0_76 subdirectory under /oracle. Alter your /home/oracle/.bash_profile to include the following:
export JAVA_HOME=/oracle/jdk1.7.0_76/jre
export PATH=$PATH:$JAVA_HOME/bin
You do need the kludge of editing refhost.xml as described in
this entry. I know this can be solved by installing redhat-lsb-core (Thank you,
Michichael), but I have problems installing it:
[root@oam ~]# yum install --skip-broken redhat-lsb-core
Setting up Install Process
Resolving Dependencies
--> Running transaction check
---> Package redhat-lsb-core.x86_64 0:4.0-7.0.1.el6 will be installed
ol6_latest/filelists | 47 MB 00:04
http://public-yum.oracle.com/repo/OracleLinux/OL6/latest/x86_64/repodata/filelists.xml.gz: [Errno -1] Metadata file does not match checksum
Finally, this should work without a glitch:
[oracle@oam ~]$ /mnt/orainst/Software/OFM/11.1.2.2.0/V43020-01/Disk1/runInstaller -jreLoc $JAVA_HOME
Starting Oracle Universal Installer...
Checking if CPU speed is above 300 MHz. Actual 3390 MHz Passed
Checking Temp space: must be greater than 150 MB. Actual 39296 MB Passed
Checking swap space: must be greater than 512 MB. Actual 5014 MB Passed
That's the result we're looking for.
Install WebLogic
Has been done before,
look at this.
Basically:
[oracle@oam ~]$ java -jar /mnt/orainst/Software/weblogic/wls1036_generic.jar
Extracting 0%....................................................................................................100%
Feb 25, 2015 2:21:26 PM java.util.prefs.FileSystemPreferences$1 run
INFO: Created user preferences directory.
Choose Custom Install, do NOT select Coherence, or Demo Database.
OAM install
Here, too, you need to alter the refhost.xml file:
Then, fire up the installer, and it will not fail to identify the OS:
[oracle@oam ~]$ /mnt/orainst/Software/OFM/11.1.2.2.0/V43017/Disk1/runInstaller -jreLoc $JAVA_HOME
Starting Oracle Universal Installer...
This takes some time, but below is what I want to see:
Ready for Configuration
First, I will configure the OUD. I'll keep it simple, just a single instance, no replication. OUD has some very nifty things, one of which is "Assured Replication". In a corporate environment, you want that!
OUD configuration
See also
this entry.
My administrator is changed to cn=oudadmin; NO SPACES - spaces will cause troubles later-on.
My root is dc=home, dc=local.
Some preparation needs to be done:
[oracle@oam ~]$ vi ./relax.sh
[oracle@oam ~]$ chmod 750 relax.sh
[oracle@oam ~]$ ./relax.sh
[oracle@oam ~]$ cat relax.sh
/oracle/middleware/asinst_1/OUD/bin/dsconfig -h oam.home.local -p 4444 \
-D "cn=oudadmin" -j ./pwdfile -n set-global-configuration-prop \
--set single-structural-objectclass-behavior:warn \
--trustAll
[oracle@oam ~]$ ldapadd -h oam -p 1389 -D cn=oudadmin -q -f prepare_oud.ldif
Please enter bind password:
adding new entry cn=Users,dc=home,dc=local
adding new entry cn=Groups,dc=home,dc=local
adding new entry cn=systemids,dc=home,dc=local
adding new entry cn=OracleAccounts,dc=home,dc=local
adding new entry cn=Users,cn=OracleAccounts,dc=home,dc=local
adding new entry cn=Groups,cn=OracleAccounts,dc=home,dc=local
adding new entry cn=Reserve,cn=OracleAccounts,dc=home,dc=local
[oracle@oam ~]$ cat prepare_oud.ldif
dn:cn=Users,dc=home,dc=local
cn:Users
objectClass:top
objectClass:orclContainer
dn:cn=Groups,dc=home,dc=local
cn:Groups
objectClass:top
objectClass:orclContainer
dn: cn=systemids,dc=home,dc=local
changetype: add
objectclass: orclContainer
objectclass: top
cn: systemids
dn: cn=OracleAccounts,dc=home,dc=local
changetype: add
objectclass: orclContainer
objectclass: top
cn: systemids
dn:cn=Users,cn=OracleAccounts,dc=home,dc=local
cn:Users
objectClass:top
objectClass:orclContainer
dn:cn=Groups,cn=OracleAccounts,dc=home,dc=local
cn:Groups
objectClass:top
objectClass:orclContainer
dn:cn=Reserve,cn=OracleAccounts,dc=home,dc=local
cn:Reserve
objectClass:top
objectClass:orclContainer
Mind you - that is the Oracle database ldapadd command. If you want to use the ldapmodify which comes with OUD, you will need to rework the ldif file.
Configure OAM
/oracle/middleware/oracle_common/common/bin/config.sh
Create a new Weblogic Domain, and select just the Entitlements Server for Admin server, Enterprise Manager, and Access Management. All other options will be selected automatically:
As I do not have a RAC install, no need for Grid Link conversion. In a corporate environment, you would not select Access manager yet, and convert the OPSS scheme to gridlink. Experience shows, you can just select all, and convert all to gridlink. You will have to watch out when you use a non-DEV prefix; select just one option, and alter the schema owner. Repeat until all schemas are done.
You would just assign the Admin server to the Unix Machine. Instead, I just do:
In the Select optional Configuration, I choose to Modify Managed Servers; I create a Unix machine, and assign both Admin Server and managed Server oam_server1 to this machine.
Now it is time to execute the mandatory patch:
[oracle@oam ~]$ cd /oracle/middleware/oracle_common/bin
[oracle@oam bin]$ ./psa
Oracle Fusion Middleware Patch Set Assistant 11.1.1.7.0
Log file is located at: /oracle/middleware/oracle_common/upgrade/logs/psa2015-02-25-16-21-20PM.log
UPGAST-00238: A dependency by component OIM on component SOA is unresolved. Upgrades of component OIM will be disabled.
A dependent component was not found while discovering upgrade components and their dependencies.
Make sure the required component has been installed.
Just select OPSS to upgrade:
Do not forget to enter "sys as sysdba" for the username...
Examine the logging in ../upgrade/logs, and make sure that the upgrade to 11.1.1.7.2 script is called successfully.
If you do NOT see this script being called, don't bother: erase and start all over again!
... ParseNexecute Script: /oracle/middleware/oracle_common/common/sql/opss/oracle/upgrade/opss_upgrade_111162_111172.sql
[2015-02-25T16:23:56.364+01:00] [RCU] [TRACE] [] [upgrade.RCU.jdbcEngine] [tid: 30] [ecid: 0000Kj1L_N^EOPWFLz3V8A1KvUXk000004,0] Adding alter statement to list:ALTER SESSION SET CURRENT_SCHEMA=DEV_OPSS
[2015-02-25T16:23:56.437+01:00] [OPSS] [NOTIFICATION] [UPGCMP-05602] [upgrade.OPSS.OPSS1] [tid: 30] [ecid: 0000Kj1L_N^EOPWFLz3V8A1KvUXk000004,0] OPSS database schema successfully updated.
[2015-02-25T16:23:56.439+01:00] [OPSS] [NOTIFICATION] [UPGCMP-05604] [upgrade.OPSS.OPSS1] [tid: 30] [ecid: 0000Kj1L_N^EOPWFLz3V8A1KvUXk000004,0] OPSS database schema is valid after update.
[2015-02-25T16:23:56.440+01:00] [Framework] [NOTIFICATION] [] [upgrade.Framework] [tid: 30] [ecid: 0000Kj1L_N^EOPWFLz3V8A1KvUXk000004,0] Component ID=OPSS, Schema=DEV_OPSS, Schema version=11.1.1.7.2, Status=VALID, Upgraded=true
Starting up...
Create the boot.properties file, so that the AdminServer starts without prompting for account info. You enter user and password in plain text, but the file gets encrypted at the first start:
[oracle@oam bin]$ cd /oracle/user_projects/domains/oam_domain/
[oracle@oam oam_domain]$ mkdir -p servers/AdminServer/security
[oracle@oam oam_domain]$ vi servers/AdminServer/security/boot.properties
It is necessary to establish the security configuration between the domain and the database. Switch to the /oracle/middleware/oracle_common/common/bin directory, and issue the following wlst command:
[oracle@oam oam_domain]$ cd /oracle/middleware/oracle_common/common/bin
[oracle@oam bin]$ ./wlst.sh /oracle/middleware/Oracle_IDM1/common/tools/configureSecurityStore.py \
> -d /oracle/user_projects/domains/oam_domain -c IAM -m create -p
Here, too, it is of critical importance that you see lines like below, and -at the end- a success message:
Feb 25, 2015 4:41:08 PM oracle.security.jps.internal.config.ldap.LdapAuditServiceConfigurator schemaCompatibleHandler
INFO: Audit store schema upgrade not required. Store Schema version 11.1.1.7.2 is compatible to the seed schema version 11.1.1.4.0
...
...
Credential store location : jdbc:oracle:thin:@oam.home.local:1521/oam.home.local
Credential with map Oracle-IAM-Security-Store-Diagnostics key Test-Cred stored successfully!
Credential for map Oracle-IAM-Security-Store-Diagnostics and key Test-Cred is:
GenericCredential
Info: diagnostic credential created in the credential store.
Info: Create operation has completed successfully.
You should now be able to start the AdminServer:
[oracle@oam bin]$ cd /oracle/user_projects/domains/oam_domain/
[oracle@oam oam_domain]$ ./startWebLogic.sh
If you want this to be speedy, give it more memory to use; the defaults are quite pathetic...
export USER_MEM_ARGS="-Xms1536m -Xmx2048m -XX:MaxPermSize=512m"
You may want to add this line to your .bash_profile file, to make sure it is set on logon time.
Configure OAM to use OUD, and more...
Ok, there are some things to configure when you want to use OAM in a corporate environment; you want OUD the be used, and you want WebLogic to use OUD as well.
Two steps are involved (see the Enterprise Delopyment Guide,
here, as long as this version lasts - Oracle tends to alter links, nowadays.)
Create two configuration files, idstore.props, and config_oam.props:
# Start idstore.props
IDSTORE_HOST: oam.home.local
IDSTORE_PORT: 1389
IDSTORE_ADMIN_PORT: 4444
IDSTORE_KEYSTORE_FILE: /oracle/middleware/asinst_1/OUD/config/admin-keystore
IDSTORE_KEYSTORE_PASSWORD: FoWK9RFOQVjok3XF78gyD05BZ1PAI80sPcqQMlRGtcWp0Ly6SD
IDSTORE_BINDDN: cn=oudadmin
IDSTORE_GROUPSEARCHBASE: cn=Groups,cn=oracleAccounts,dc=home,dc=local
IDSTORE_SEARCHBASE: dc=home,dc=local
IDSTORE_USERNAMEATTRIBUTE: cn
IDSTORE_LOGINATTRIBUTE: uid
IDSTORE_USERSEARCHBASE: cn=Users,cn=oracleAccounts,dc=home,dc=local
IDSTORE_NEW_SETUP: true
POLICYSTORE_SHARES_IDSTORE: true
# OAM
IDSTORE_OAMADMINUSER:oamadmin
IDSTORE_OAMSOFTWAREUSER:oamLDAP
OAM11G_IDSTORE_ROLE_SECURITY_ADMIN:OAMAdministrators
# OAM and OIM
IDSTORE_SYSTEMIDBASE: cn=systemids,dc=home,dc=local
# OIM
#IDSTORE_OIMADMINGROUP: OIMAdministrators
#IDSTORE_OIMADMINUSER: oimLDAP
# WebLogic
IDSTORE_WLSADMINUSER : weblogic_idm
IDSTORE_WLSADMINGROUP : WLSAdmins
### end idstore.props
###############
### start config_oam.props
# Note: Two parameter settings determine whether you are
# configuring Access Manager with Oracle Identity Manager integration
# or Access Manager alone.
# To configure Access Manager with Oracle Identity Manager
# integration, set OAM11G_OIM_INTEGRATION_REQ to true and
# specify a value for OAM11G_OIM_OHS_URL.
# To configure Access Manager without Oracle Identity Manager,
# set OAM11G_OIM_INTEGRATION_REQ to false.
# These parameters are used to add extra links, such as Forgotten
# Password, to the Access Manager credential collection page
# If you configure Access Manager without Oracle Identity Manager,
# then decide to add Oracle Identity Manager at a later date, you must
# run this command again to configure Access Manager with Oracle
# Identity Manager integration.
WLSHOST: oam.home.local
WLSPORT: 7001
WLSADMIN: weblogic
WLSPASSWD: weblog1c
IDSTORE_DIRECTORYTYPE: OUD
IDSTORE_HOST: oam.home.local
IDSTORE_PORT: 1389
IDSTORE_BINDDN: cn=oudadmin
IDSTORE_USERNAMEATTRIBUTE: cn
IDSTORE_LOGINATTRIBUTE: uid
OAM11G_SERVER_LOGIN_ATTRIBUTE: uid
IDSTORE_USERSEARCHBASE: cn=Users,cn=oracleAccounts,dc=home,dc=local
IDSTORE_SEARCHBASE: cn=oracleAccounts,dc=home,dc=local
IDSTORE_GROUPSEARCHBASE: cn=Groups,cn=oracleAccounts,dc=home,dc=local
IDSTORE_SYSTEMIDBASE: cn=systemids,dc=home,dc=local
IDSTORE_OAMSOFTWAREUSER: oamLDAP
IDSTORE_OAMADMINUSER: oamadmin
PRIMARY_OAM_SERVERS: oam.home.local:5575
WEBGATE_TYPE: ohsWebgate11g
ACCESS_GATE_ID: AdminWG
# OAM11G_OIM_WEBGATE_PASSWD: password to be assigned to WebGate
COOKIE_DOMAIN: .poc.local
OAM11G_WG_DENY_ON_NOT_PROTECTED: true
OAM11G_IDM_DOMAIN_OHS_HOST: webgate.home.local
OAM11G_IDM_DOMAIN_OHS_PORT: 7777
OAM11G_IDM_DOMAIN_OHS_PROTOCOL: http
OAM11G_SERVER_LBR_HOST: wegbate.home.local
OAM11G_SERVER_LBR_PORT: 7777
OAM11G_SERVER_LBR_PROTOCOL: http
OAM11G_OAM_SERVER_TRANSFER_MODE: open
OAM_TRANSFER_MODE: open
OAM11G_IDM_DOMAIN_LOGOUT_URLS:/console/jsp/common/logout.jsp,/em/targetauth/emaslogout.jsp
OAM11G_IDSTORE_ROLE_SECURITY_ADMIN: OAMAdministrators
OAM11G_IDSTORE_NAME: OUDInternalStore
OAM11G_SSO_ONLY_FLAG: false
COOKIE_EXPIRY_INTERVAL: 120
OAM11G_IMPERSONATION_FLAG: false
OAM11G_OIM_INTEGRATION_REQ: false
# OAM11G_OIM_OHS_URL:https://ZZZZZZ.home.local:443
SPLIT_DOMAIN:true
I am not going into any detail - see the manuals what these variables mean. Just pointing out TRANSFER_MODE would be simple, or even certificate, in a corporate environment - it makes sure Oracle Access Protocol (OAP) is used to encrypt traffic between OAM and the Webgates.
This *may* affect the ease of connecting Mobile Apps, so I will leave it at "OPEN" for now.
Run the wizards:
export MW_HOME=/oracle/middleware
export ORACLE_HOME=/oracle/middleware/Oracle_IDM1
echo $JAVA_HOME
cd /oracle/middleware/Oracle_IDM1/idmtools/bin/
./idmConfigTool.sh -preConfigIDStore input_file=~/idstore.props
./idmConfigTool.sh -prepareIDStore mode=WLS input_file=~/idstore.props
./idmConfigTool.sh -prepareIDStore mode=OAM input_file=~/idstore.props
[oracle@oam bin]$ ./idmConfigTool.sh -configOAM input_file=~/config_oam.props
Enter ID Store Bind DN password :
Enter User Password for OAM11G_IDM_DOMAIN_WEBGATE_PASSWD:
Confirm User Password for OAM11G_IDM_DOMAIN_WEBGATE_PASSWD:
Enter User Password for IDSTORE_PWD_OAMSOFTWAREUSER:
Confirm User Password for IDSTORE_PWD_OAMSOFTWAREUSER:
Enter User Password for IDSTORE_PWD_OAMADMINUSER:
Confirm User Password for IDSTORE_PWD_OAMADMINUSER:
Connecting to t3://oam.home.local:7001
Connection to domain runtime mbean server established
Starting edit session
Edit session started
Connected to security realm.
Validating provider configuration
Validated desired authentication providers
Created OAMIDAsserter successfuly
Created OUDAuthenticator successfuly
Setting attributes for OUDAuthenticator
All attributes set. Configured inOUDAuthenticatornow
LDAP details configured in OUDAuthenticator
Control flags for authenticators set sucessfully
Reordering of authenticators done sucessfully
Saving the transaction
Transaction saved
Activating the changes
Changes Activated. Edit session ended.
Connection closed sucessfully
The tool has completed its operation. Details have been logged to automation.log
As you can see the last command reconfigures WebLogic; you will have to stop and start the stack...(and no: spelling errors do appear, this is cut-n-paste)
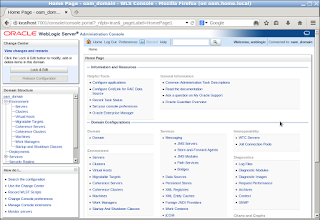
Then, change the WebLogic Identity Providers; log on to the weblogic console (at http://yourhost:7001/console), navigate to Security Realms, myrealm:
First of all, make sure all of them are SUFFICIENT, not REQUIRED. REQUIRED means this authentication step
must be satisfied, despite all others. I find one is enough.
Change REQUIRED to SUFFICIENT.
Repeat for all providers:
Bug 13824816 workaround
After restarting, log on to the WLS Console, and navigate to myrealm again. Open the "Roles and Policies" tab, expand Global Roles, and then Roles:
Click on the Roles link, and add OAMAdministrators and WLSAdmins as groups:
Modify access, and make yourself administrator
First, add yourself to the group of internal users (cn=Users,cn=OracleAccounts,dc=home,dc=local); create a file with the following contents:
dn: cn=frank,cn=Users,cn=OracleAccounts,dc=home,dc=local
objectclass: orcluserV2
objectclass: person
objectclass: inetorgperson
objectclass: organizationalPerson
objectclass: orcluser
objectclass: top
givenName: Frank
uid: frank
cn: frank
sn: Van Bortel
userPassword: ******
mail: *******
orclSAMAccountName: frank
Load it into ldap:
[oracle@oam ~]$ /oracle/db/product/11.2.0/bin/ldapadd -h oam -p 1389 -D cn=oudadmin -q -f ./frank.ldif
Please enter bind password:
adding new entry cn=frank,cn=Users,cn=OracleAccounts,dc=home,dc=local
Now, create the following ldif file, and load it into the LDAP server:
dn: cn=WLSAdmins,cn=Groups,cn=oracleAccounts,dc=home,dc=local
changetype: modify
add: uniquemember
uniquemember: cn=frank,cn=Users,cn=OracleAccounts,dc=home,dc=local
dn: cn=OAMAdministrators,cn=Groups,cn=oracleAccounts,dc=home,dc=local
changetype: modify
add: uniquemember
uniquemember: cn=frank,cn=Users,cn=OracleAccounts,dc=home,dc=local
[oracle@oam ~]$ /oracle/db/product/11.2.0/bin/ldapmodify -h oam -p 1389 -D cn=oudadmin -q -f ./add_frank.ldif
Please enter bind password:
modifying entry cn=WLSAdmins,cn=Groups,cn=oracleAccounts,dc=home,dc=local
modifying entry cn=OAMAdministrators,cn=Groups,cn=oracleAccounts,dc=home,dc=local
You should now be able to see yourself in the list of users in Weblogic. Even better, you should be able to log on with your own account (as defined in frank.ldif):
If the above does not work, check the OUDAuthenticator properties; it should be defined as an iPlanet directory server (that is what Sun called it, before Oracle bought Sun, and renamed the by then called Sun Enterprise Directory Server to ODSEE, and then to OUD).
It usually gets -oh magic- defined as an Open LDAP server. It has definition errors, one of which is in group definition; it uses GroupOfNames, not GroupOfUniqueNames (capitalization not needed). If you find that your group search uses wrong attribute names, make sure to correct that.
You should be able to see that your account belongs the WLSAdmins group (as well as the OAMAdministrators).
The faulty attribute names prevent that.
You should also be able to log on to the OAM Administration Console (at http://oam.home.local:7001/oamconsole) with your personal account, and discover you now have 5 webgates!
Webgate install
In the configuration wizard part, I specified OAM11G_SERVER_LBR_HOST: wegbate.home.local. That does not exist, yet.
This is how to install a webgate (assuming you have downloaded WebTier V11.1.1.7, and V43022: WebGates 11.1.2.2.0):
Start the installer to install the Oracle HTTP server:
/mnt/orainst/Software/OFM/WebTier/11.1.1.7.0/Disk1/runInstaller
Skip the updates, choose "Install Software - do NOT configure"
Leave all else default, done.
Now, it is time for the WebGate software:
/mnt/orainst/Software/OFM/11.1.2.2.0/V43022-01/Disk1/runInstaller -jreLoc /oracle/jdk1.7.0_76/jre
Skip the software updates, ignore checks, leave all default, done.
Configure
/oracle/middleware/Oracle_WT1/bin/config.sh
Deselect all, but the HTTP server; I don want the overhead of WebCache, or WebLogic server and domains.
Change the install directory to /oracle/middleware/Oracle_WT1/ecc1, and the instance name accordingly: ecc1. Next, no updates, configure, done.
You should now have a response when you point the browser to oam:7777.
Time for a virtual host
I need to rework the OHS to respond to webgate:7777, not oam:7777.
In order to do that, I need to add that as an alias to the hosts file, /etc/hosts.
Change:
192.168.4.222 oam oam.home.local
into:
192.168.4.222 oam oam.home.local webgate webgate.home.local
I can now browse to http://oam:777/index.html, or webgate:7777/index.html.
However, in order to make sure all redirects, etc, end up where thet came from, I need to tell the HTTP server webgate.home.local is a valid name, too.
The configuration now simply states listen to all addresses, port 7777. That is not how things ought to be.
So, alter the Listen directive in httpd.conf:
# OHS Listen Port
Listen oam.home.local:7777
Move to the moduleconf directory, and move plsql.conf to ../disabled/
Then, create a vh.conf file with the following content:
<VirtualHost *:7778>
ServerName webgate.home.local
RewriteEngine On
RewriteOptions inherit
ServerAdmin me@home.local
# DocumentRoot "${ORACLE_INSTANCE}/config/${COMPONENT_TYPE}/${COMPONENT_NAME}/webgate"
</VirtualHost>
I just redefined the virtual host to listen to another port, too. Just to show the difference between the default host, and the virtual host.
Configure the WebGate
Circumvent “a known bug for 11.1.2.2.0 OHS Webgate” (Doc ID 1678062.1):
cd /tmp
/oracle/jdk1.7.0_76/bin/jar xvf /mnt/orainst/Software/OFM/11.1.2.2.0/V43022-01/Disk1/stage/Components/oracle.as.oam.webgate.ohs_linux64/11.1.2.2.0/1/DataFiles/filegroup1.jar webgate/ohs/lib/libxmlengine.so
/oracle/jdk1.7.0_76/bin/jar xvf /mnt/orainst/Software/OFM/11.1.2.2.0/V43022-01/Disk1/stage/Components/oracle.as.oam.webgate.ohs_linux64/11.1.2.2.0/1/DataFiles/filegroup1.jar webgate/ohs/lib/webgate.so
/oracle/jdk1.7.0_76/bin/jar xvf /mnt/orainst/Software/OFM/11.1.2.2.0/V43022-01/Disk1/stage/Components/oracle.as.oam.webgate.ohs_linux64/11.1.2.2.0/1/DataFiles/filegroup1.jar webgate/ohs/tools/setup/InstallTools/EditHttpConf
cp webgate/ohs/lib/* /oracle/middleware/Oracle_OAMWebGate1/webgate/ohs/lib/
cp webgate/ohs/tools/setup/InstallTools/EditHttpConf /oracle/middleware/Oracle_OAMWebGate1/webgate/ohs/tools/setup/InstallTools/
Of course, your directory structure may differ...
cd /oracle/middleware/Oracle_OAMWebGate1/webgate/ohs/tools/deployWebGat
./deployWebGateInstance.sh -w /oracle/middleware/Oracle_WT1/ecc1/config/OHS/ohs1 -oh /oracle/middleware/Oracle_OAMWebGate1
Response: Copying files from WebGate Oracle Home to WebGate Instancedir
export LD_LIBRARY_PATH=$LD_LIBRARY_PATH:/oracle/middleware/Oracle_WT1/lib:/oracle/middleware/Oracle_OAMWebGate1/webgate/ohs/lib/
cd /oracle/middleware/Oracle_OAMWebGate1/webgate/ohs/tools/setup/InstallTools
./EditHttpConf -w /oracle/middleware/Oracle_WT1/ecc1/config/OHS/ohs1 -oh /oracle/middleware/Oracle_OAMWebGate1/
Response: The web server configuration file was successfully updated
/oracle/middleware/Oracle_WT1/ecc1/config/OHS/ohs1/httpd.conf has been backed up as /oracle/middleware/Oracle_WT1/ecc1/config/OHS/ohs1/httpd.conf.ORIG
If you now point to webgate:777/index.html, you will get an HTTP-500 status back: Internal Server Error. This is due to the fact wegbate ecc1 is now active, but there is no connection to the OAM server. Yet.
So, not in a day...
OK, it's been a long day, and not everything is done yet. But you do have a framework; OAM is there, as well as OUD and the database (which is used for Authentication (AuthN) and Authorization (AuthZ) Policies, by the way).
Left to be done is the registration of the WebGate in OAM, and fixing the Perl-based login pages, so that I can actually see a resource being protected.
The difference between Embedded Credential Collector (ECC) as one mechanism, and Detached Credential Collector (DCC) with a Resource Protecting Webgate (RPW) as another is also left for tomorrow. Well... another entry.